Chess.com is a site where people from all over the world can play chess and socialize with each other. It currently has over 150 million users. Unfortunately, it recently suffered a data breach where the information of over 800,000 users was compromised.
A person operating under the alias ‘DrOne’ has claimed responsibility for leaking the scraped database of Chess.com containing the personal data of the site’s users. The attacker shared information about the data breach on November 8th on the popular site Breach Forums.
If you’re a chess enthusiast and frequently use Chess.com, then we highly recommend that you update your passwords and keep yourself up-to-date with any news that’s coming out about the data breach in the next few days. Here’s a quick rundown of what happened.
What Information Has Been Compromised?
According to Hackread.com, who also reported a LinkedIn data breach on the site Breach Forum, the leaked information includes details like:
- Full names
- Usernames
- Profile links
- Email addresses
- Users’ countries of origin
- Avatar URLs and profile pictures
- User IDs
- Date of registration
The combination of full names, usernames, profile links, countries, email addresses, and other details in the leaked Chess.com data provides abundant information for cybercriminals to carry out identity theft, phishing campaigns, and social engineering schemes.
While the database fortunately does not contain passwords, nearly all of the leaked email addresses were valid and active on existing Chess.com accounts. When attempts were made to register new accounts using the emails, error messages appeared stating that an account already existed with that address.
This confirms that the breach exposed actual user information tied to real Chess.com accounts, rather than outdated or fake data. Even without passwords, the leaked details are enough for criminals to convincingly impersonate users in phishing emails or fraudulent communications. The data also allows cross-referencing with past credential leaks to more easily guess passwords.
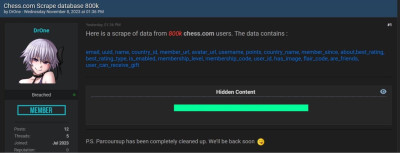
Announcement of the data breach on Breach Forum. (source: hackread.com)
How the Information Was Obtained
The Chess.com data was likely obtained through a process known as web scraping or data scraping. This involves using automated software to extract information from websites.
For a major site like Chess.com, blocking scrapers can be extremely difficult. Websites may use captcha tests or limit how often the same IP address can access pages, but scrapers frequently find ways around these defenses.
Scraping can serve legitimate research purposes in some cases. Academic studies may gather public data to analyze social networks or train machine learning algorithms. However, scraping becomes unethical and illegal when it infringes on privacy, violates terms of service, or is used for criminal purposes.
In this case, the scraper extracted private user details at a large scale without permission. Chess.com will need to identify vulnerabilities in their defenses against scraping and improve safeguards. But with constantly evolving scraper techniques, no solution will be perfect. This incident highlights inherent risks websites face in the cat-and-mouse game against data scraping.
Implications for Chess.com Users
This data breach creates substantial risks for Chess.com users now vulnerable to identity theft, phishing scams, and other cyber threats.attackers. It is critical that users take action to secure their accounts in the wake of this incident.
If you’ve been affected by the breach, we highly recommend that you install an antivirus such as TotalAV and immediately change your password. Make sure you change it on other sites as well. Never use the same password on multiple sites as this can allow hackers to easily gain access to your data.
Users should also beware of phishing attempts seeking to capitalize on the breach. Cybercriminals may send spoofed emails pretending to be Chess.com and containing malicious links or attachments. To avoid falling victim, scrutinize the full URL before clicking by hovering over the link and look out for slight misspellings or odd domains.
While no single solution can eliminate risk from the leaked data, following cybersecurity best practices around unique passwords and identifying phishing attempts can help users defend themselves after this breach. Chess.com must also strengthen its defenses and user awareness to prevent such incidents in the future.
Keep Your Data Safe
This breach represents a serious security incident for Chess.com and a potential threat to its users. By taking proactive steps to update passwords and recognizing phishing attempts, users can help protect their accounts and personal information.
Chess.com also needs to determine how the data was accessed and implement stronger protections against scraping vulnerabilities. For now, just don’t respond to any suspicious emails and make sure you don’t open any links that have come from sources you don’t trust.